DORA's TLPT Mandate: Is Your Bank Ready?

Yesterday, I had a meeting with an international consulting firm about the Digital Operational Resilience Act (DORA), which officially comes into effect tomorrow on January 17, 2025. This new regulation will significantly impact banks worldwide that have branches in Europe. Among its many requirements, it introduces something that caught my attention: Threat-Led Penetration Testing (TLPT).
But what is TLPT, and who needs It?
Simply put, TLPT is a type of red teaming . But when does it apply, and how does it work?
Firstly, TLPT applies to all banks with a presence in the EU. If the bank's IT is located outside the EU, then the testing will apply to the entire bank group, including all its branches globally (full scope). However, if the bank is contacted by the financial regulation authority of the country where it has its IT, then the scope will only be the branch of this specific country.
Things can get a bit tricky here. Let’s say your bank operates in both Germany and France. It’s possible that France’s regulatory authority may decide not to require a TLPT, while Germany’s does. It’s also worth mentioning that TLPT primarily targets large institutions—those considered “too big to fail” or handling a certain volume of payment transactions. Smaller banks are generally not in scope.
But for those required to perform a TLPT, the timeline is strict: it lasts 6 months so you cannot wait to receive the letter from the regulator to conduct it, and it must be conducted every three years at a minimum. However, if the financial regulator deems a TLPT unsatisfactory, it can request a redo, potentially sooner than planned, yes...
In the end, it's a bit like the ISO27001 certification, you have a scope and you have to maintain it.
TLPT... Beyond a Standard Red Team Exercise
So, what exactly is a TLPT? Unlike a regular red teaming exercise, TLPT follows the TIBER-EU framework and involves multiple teams, each with specific roles to ensure independence.
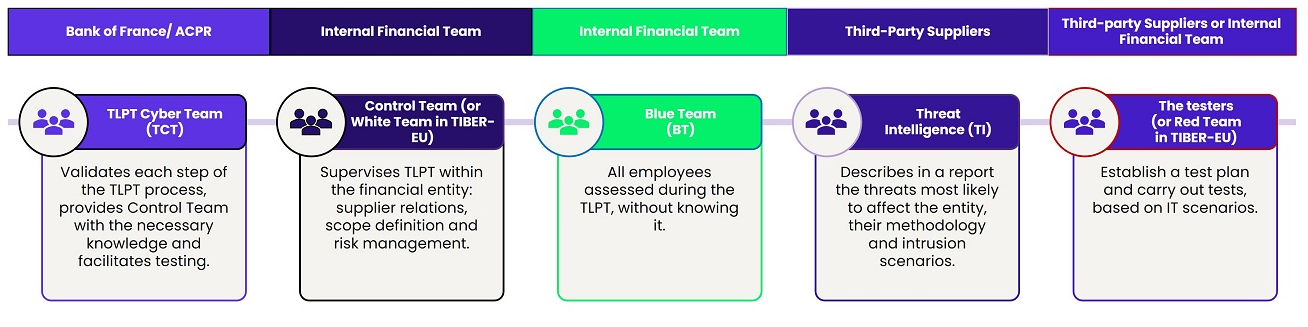
Here’s a breakdown:
- The Financial Regulator’s TLPT Cyber Team
This team oversees the entire process, validating each step and ensuring independence among the involved teams. For instance, the blue team (defenders) cannot also act as the white team (facilitators) because it would compromise the simulation of real attack if they know when they are attacked. Similarly, the purple team (threat intelligence) must be distinct from the red team (attackers) to avoid any conflict of interest—otherwise, it would be like the red team setting its own attack scenarios. - The White Team
This is the bank’s internal team responsible for coordinating the TLPT. They act as facilitators, ensuring smooth communication and managing all stakeholders. Typically, this is the bank’s cyber security team. - The Blue Team
These are the defenders, this team is kept unaware of the exercise, allowing them to respond to the red team’s attacks as they would in a real-world scenario. Their goal is to detect, contain, and eradicate the red team from the network while protecting the bank’s systems. In banks without internal SOC, the blue team may be an MSSP. - The Purple Team
This is the cyber threat intelligence (CTI) team which identifies attack scenarios based on the tactics, techniques, and procedures (TTPs) of threat actors targeting the bank and its country. Using frameworks like MITRE ATT&CK and the Cyber Kill Chain, the purple team develops realistic attack scenarios. Their research typically takes 4–6 weeks. - The Red Team
Finally, the red team executes the attack scenarios crafted by the purple team, emulating real-world adversaries. Their testing phase usually lasts a minimum of 12 weeks, with clear objectives like gaining domain admin access, accessing sensitive CEO mailbox, or testing data exfiltration. However, certain actions—such as disrupting bank systems—are strictly off-limits.
At the end of the exercise, the red team compiles a detailed report for the white team and the financial regulator. Based on the results, the regulator may:
- Validate the test and schedule the next one in 2–3 years.
- Request a redo of the TLPT if it was unsatisfactory.
- Fine or take further action if the bank’s security posture is deemed inadequate.
To conclude, I believe the DORA regulation, and specifically the TLPT, is a positive step forward in strengthening the cyber security posture of financial institutions. By mandating GRC and exercises like the TLPT, regulators are addressing the reality of today's cyber threat landscape. That said, one must recognize that TLPT is not without difficulty. It demands significant financial cost and human resources, which may even strain large banks. And still, for banks safety and customer trust, I guess it's worth the price.
References
[1]: https://www.eiopa.europa.eu/digital-operational-resilience-act-dora_en
[2]: https://tiber-eu.fr/
Member discussion